When U.S. Cybersecurity Funding Stops, Canada’s Banks Pay the Price
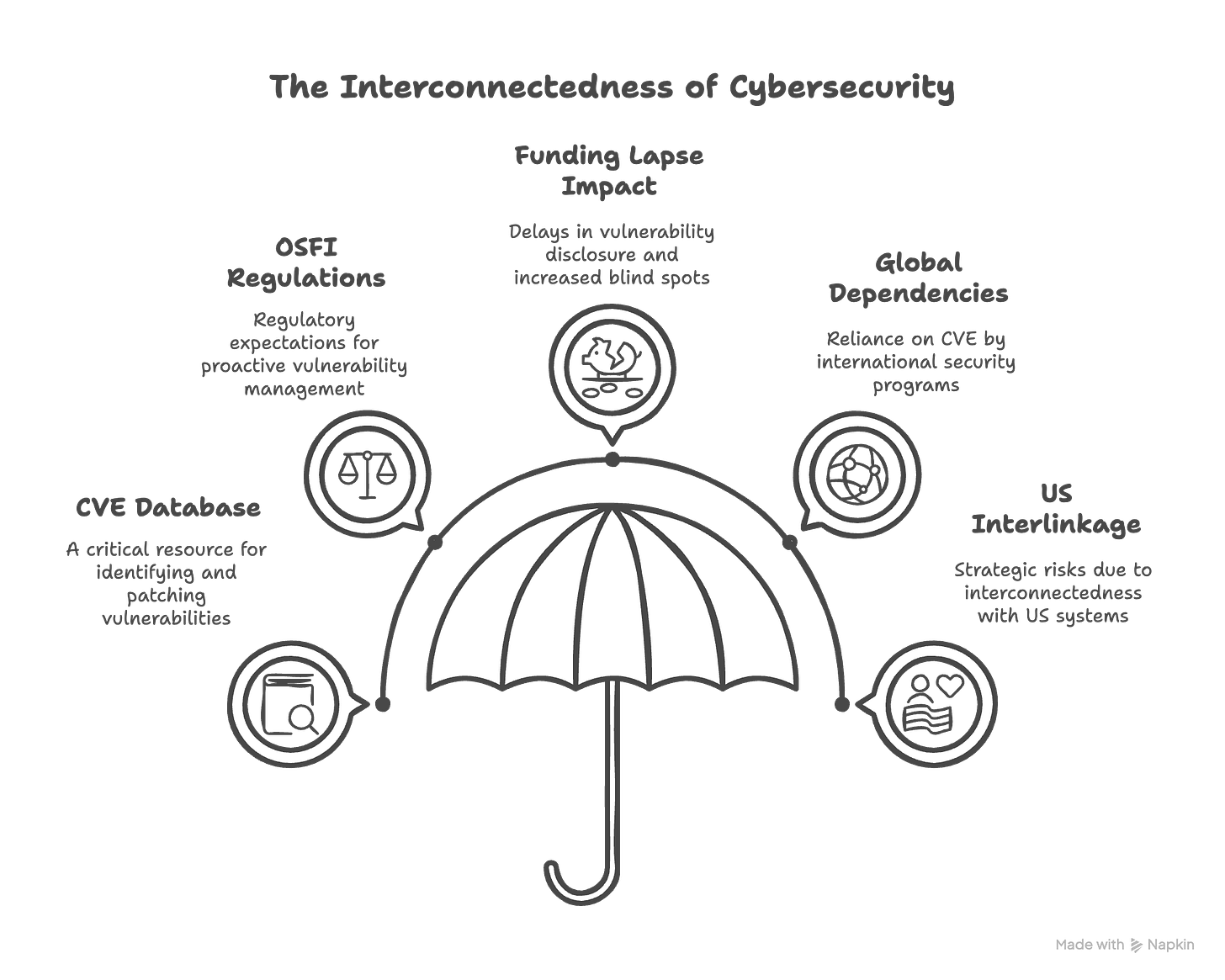
Critical cybersecurity threats often lurk beneath the headlines, unnoticed until it's too late. Recently, the US experienced a brief lapse in funding for the Common Vulnerabilities and Exposure (CVE) program, posing a strategic risk for Canadian Financial Institutions. Here's why it matters, what's at stake, and how your institution can proactively navigate the fallout.
Why This Matters
Canadian banks, insurance firms, and fintech companies routinely reference the CVE database to identify and patch vulnerabilities, guiding security investments and assessments.
OSFI's cybersecurity regulations expect proactive vulnerability management aligned with recognized standards—often implicitly relying on stable CVE frameworks.
The lapse in funding means delays in vulnerability disclosure, slower patches, and increased cybersecurity blind spots in Canada.
CVE underpins many security programs and tools including MITRE, NIST, and is a dependency for Japanese and European Vulnerabilities Databases.
Canadian cybersecurity programs (Western world for the most part) are heavily interlinked with US systems and that creates a strategic risk.
When your risk database is someone else’s budget item
The Bank of Canada has listed cyber risks as the number 2 risk for Canadian financial institutions, ironically right behind trade war. Traditionally, the US has been the leader for cyber programs, and we adopt many of their recommendations. From vulnerability databases to frameworks for implementations such as Zero Trust to security tooling. With the current US government's erratic approach to cutting funding for programs, it does raise a risk to any entities that are adopting these going forward.
The immediate impact felt through Canadian financial institutions would include:
Financial Standards (OSFI, PCI DSS) - OSFI's B-13 guideline requires financial institutions to regularly scan, identify, and rank vulnerabilities. A standard such as CVE/NVD both of which are American are used as reputable sources. These assume that up-to-date information is available, which could have been risked in this case.
Critical Infrastructure - The financial sector is considered one of the critical infrastructure sectors within Canada. But even national databases and advisories are based on CVE. Protecting our critical infrastructure means we need alternative plans.
International Standard - many of other international vulnerability standards including European and Japanese are also impacted by CVEs.
This all equates to potentially slower patch updates, less reliable vulnerability intelligence, and increased cybersecurity uncertainty. This is precisely why Canadian Financial Institutions cannot rely on funding from US entities and need to explore alternatives.
Increased exposure during geopolitical tensions
In times of geopolitical tension, the cybersecurity landscape becomes even more precarious. The lapse in funding for critical databases like the CVE program coincides with an era of heightened cyber threats from nation-state actors such as China, Russia, and Iran. These actors are known for their sophisticated cyber tactics and persistent targeting of critical infrastructure, including financial institutions.
Canadian financial institutions would be vulnerable without timely updates and disclosures from the CVE program which could lead to increased susceptibility to exploitation. With delayed patches and less reliable vulnerability intelligence, these institutions face a higher risk of cyber attacks that could disrupt operations and compromise sensitive data.
During geopolitical tensions, the risk of cyber espionage and attacks escalates. Nation-state actors often exploit vulnerabilities to gain strategic advantages and disrupt critical infrastructure. For Canadian banks and financial institutions, this means a potential increase in cyber incidents that could have far-reaching consequences for the economy and national security.
Exploring alternatives to CVE
I've mentioned throughout the article that CVEs are linchpin to cyber initiatives across Western countries. So, what alternatives do we have today? In the short term, funding issues were resolved, that means access to timely cyber information still is available.
For the long run, the best option would be to look at alternative funding models for the program which benefits multiple countries, critical infrastructure sectors, security tool vendors, in fact the entire industry. In fact, the CVE foundation has begun to explore alternatives such as diversified funding and endowment funds. I would argue all member states of five eyes should be contributing to the foundation, and arguably it doesn't need to reside within a single country. That way should the focus of a single country shift towards domestic focus, it doesn't affect all other countries. Canada's policy should focus on increasing our resiliency and building a stronger say in the global economy.
Canadian financial institutions must develop fallback plans that ensure continuity and resilience in the face of cybersecurity challenges. This includes exploring alternative sources of vulnerability intelligence, investing in independent cybersecurity frameworks, and strengthening partnerships with international allies to share insights and resources. It's time to leverage our partners to increase visibility into potential cyber risks.