Making sense of Zero Trust as a Platform Engineer
As the bridge between Development, Cybersecurity and Business, your job is to implement Zero Trust. So why and where do you start?
Recently a group of Chinese threat actors, Salt Typhoon, hacked 8 telecom networks in the US; it has been labelled as the worst telecom hack in US history. Given the increasing frequency of cybersecurity incidents, it's now more imperative than ever to design systems for such scenarios. While Critical National Infrastructure (energy, telecommunications, finance, defense) has a higher chance of being targeted, they aren't the only ones at risk.
We need to contend with an evolving landscape of cybersecurity threats with more complex attack vectors. Additionally, business infrastructure footprint has grown with it being common to have multi-cloud and hybrid environments. Platform Engineers need to worry not just about the security within CI/CD lifecycle but across underlying systems.
The reason why this is important to Platform Engineers is because they are often the ones that are tasked with being the ones that have to put the various pieces together navigating cybersecurity professional recommendations, developer issues and business desires.
This article is meant for those of us tasked with making it all work, and how we architect these systems to be secure.
The issue with traditional security
The traditional design with on-premise networks was to design a security moat (like those around a castle) to make it difficult to infiltrate the organization's systems. The issue with moats is while they are great at keeping intruders out, once the intruders enter they have full (or close to) access to everything.
That's not the only flaw with this design. In modern systems not all applications and services can be behind a moat. Common scenarios for breaking the moat are:
Having bring-your-own device policies meaning people are able to access company data on their personal phones, tablets, and more. These devices often won't have uniform policies and controls applied on them.
Using SaaS products meaning limited access to the security of those systems (single sign-on doesn't equate to secure)
Integrating 3rd party APIs such as ChatGPT and other LLMs into your services. These systems data security controls are necessarily aligned with your organizations.
With modernization, traditional security is insufficient. In fact, with upcoming shifts in the market from blockchain systems redefining web to AI shifts causing autonomous transformations traditional security is downright dangerous.
A better approach is required.
Never Trust, Always Verify
Zero Trust focuses on building security into the architecture of modern systems, with the underlying principle being "never trust, always verify". What this means is:
Systems need to be designed with the notion of "if breached how can we limit the damage and maintain business operations?"
Use the principle of least privilege, provide dynamic a security policy, and on a per-session basis - few people likely need full control over resources and even if they do, it can be done with just-in-time (short-term) and just-enough access (subset of resources).
Verify that any request is authorized and authenticated in a be dynamic and strictly enforced. This means using data such as location, devices, and identity become imperative as factors to validate access
The business measures & monitors the security posture of all assets, and uses this information to improve security posture.
All communication is secured.
By having a never trust, always verify approach to systems, it reduces the impact when the system gets compromised.
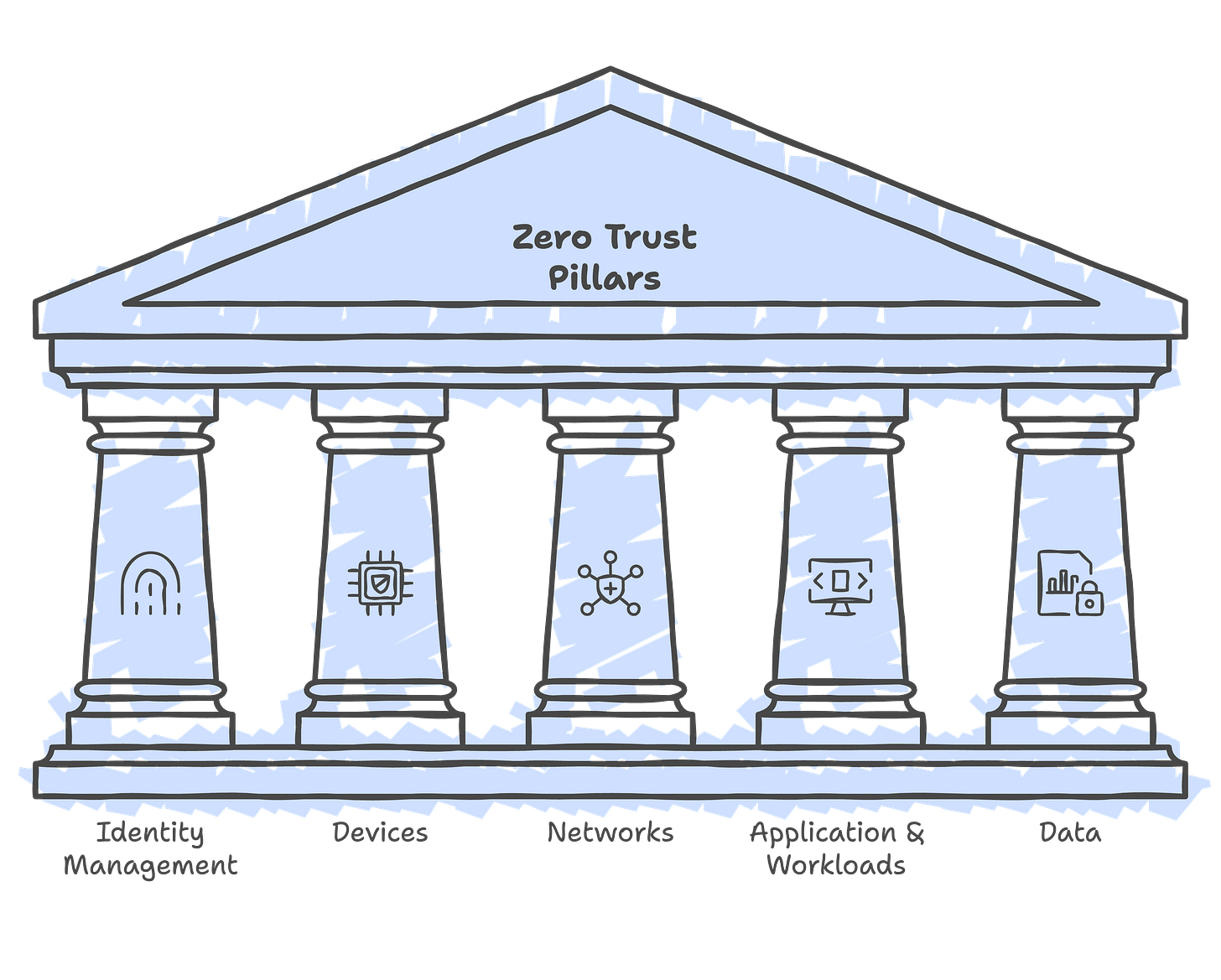
Zero Trust Pillars
The idea of the pillars within zero trust is to give holistic coverage in all your environments. There are 5 core pillars to evaluate for zero trust. They are:
Identity
Devices
Networks
Applications & workloads
Data
Each pillar represents a critical dimension of an organization's security strategy, working together to create a comprehensive, adaptive defense mechanism that leaves no aspect of a digital ecosystem unprotected.
Here is a breakdown of each of the pillars:
Identity - This is the foundation of Zero Trust, and focuses on verifying and managing identities (can include users and entities). The goal here is only the right identity can access resources at the right time.
Devices - Refers to assets including hardware, firmware, and software. This will include everything from IoT devices, servers, laptops to patch management, device compliance.
Networks - The backbone for communication of all systems, the goal is to move beyond perimeter-based security. It focuses on micro-segmentation based on application profiles, granular access controls, traffic management within the network, encryption of traffic, and network resiliency.
Applications & Workloads - Software and services that run on systems. This includes legacy and modern cloud-native applications. A lot of DevSecOps and AppSec best practices fit in here both from the securing during development to monitoring and providing threat protection to live applications.
Data - The ultimate goal for protection is to safeguard data. It covers scenarios such as encryption, data inventory management, tracking data movement, and applying context-aware protection based on data sensitivity.
The ideal state of these pillars need to have automation & orchestration setup (in a very mature and robust environment) because it becomes difficult to manage thousands of resources without having processes, visibility, analytics and governance. While this ideal state seems daunting now, the best time to start is now and work to implement, evaluate and improve over time.
Planning your rollout
There is no single product that you can purchase to achieve optimal zero trust security. Rolling out zero trust practices takes time. Even if it is a greenfield environment where such protections can be easily applied (from the onset), the team may not have the needed resources, capacity, or capability to rollout all components. These issues are exasperated for brownfield environments.
Start by assessing where in its zero trust journey the organization is currently, ideally you want to achieve an optimal state in all 5 pillars. Reality works differently, it's a negotiation with the business to understand where efforts are going to focus. The business may have other priorities over the next few months than security alone.
Your progress for some pillars may be traditional while others advanced state of maturity. In my experience, the hardest part is to get started (and really look at the skeletons in the closet), but once you begin reaching the next level of maturity is often easier. Buy-in from business, developers and even your own team can often be difficult.
So where do we begin? The following 5 steps are a great way to approach on building it out:
Define the protection surface - Rolling out everything to all resources in your system isn't viable given that a surface includes data, assets, applications and services. Narrow the focus and implement low hanging fruit so that it builds momentum and gives the team time to understand the nuances. Even if a partial understanding is reached and can be implemented start with that and iterate.
Map transaction flows - This helps to build an application profile (and understand where systems are vulnerable) and that information will be used to develop maturity within your pillars.
Build your Zero Trust architecture - With a full understanding of the protection surface and transition flows, an iterative design of the system architecture can be put together to meet zero trust maturity goals.
Develop Automated Policies - These provide governance and visibility (monitoring and analytics) into deployed resources.
Monitor and Maintain - as mentioned earlier in the article, to keep this zero trust current one needs to measure the security of all assets and use this to improve our security posture and evolve the architecture as required.
Unfortunately Zero Trust is not a one time activity, but more akin to a way of life. With breaches becoming more common, it is only a matter of time before it impacts your organization. The best time to start is now.